The ESP32 Marauder is a WiFi and Bluetooth analysis tool. It hosts a suite of capabilities for frame capture, device enumeration, and frame transmission. It is intended to serve as a portable device to stand in for physically larger traffic capturing tools and to provide captured data for post-op analysis.
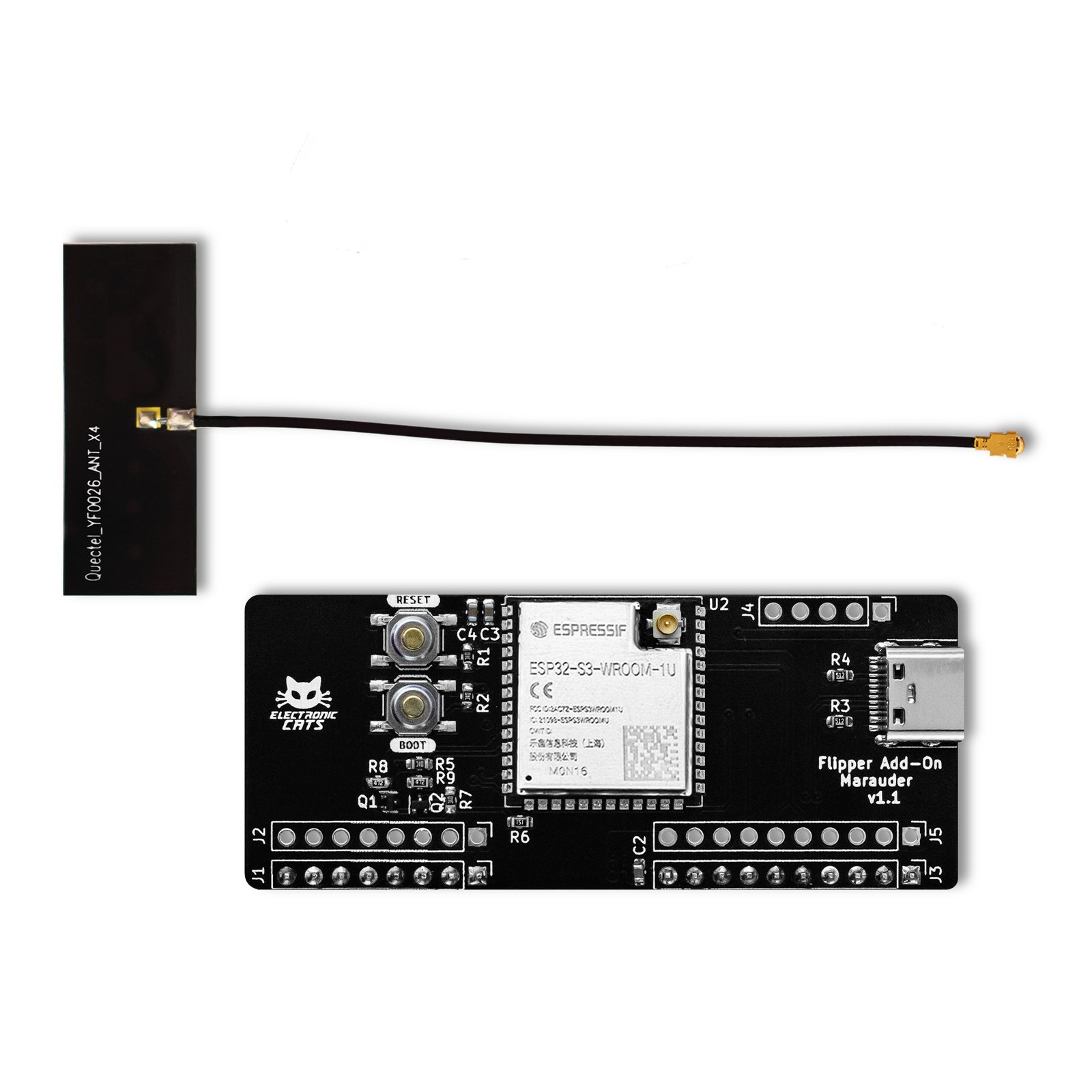
This Add-On unlocks a powerful toolset for the Flipper, fueled by the ESP32-S3 module and meticulously crafted for offensive and defensive maneuvers in the WiFi and Bluetooth realms.
ESP32-S3 supports 2.4 GHz Wi-Fi (802.11 b/g/n) with 40 MHz of bandwidth support. The Bluetooth Low Energy subsystem supports long-range through Coded PHY and advertisement extension. It also supports higher transmission speed and data throughput, with 2 Mbps PHY. Both Wi-Fi and Bluetooth LE have superior RF performance that is maintained even at high temperatures.
Tech Specs
ESP32-S3
- Xtensa® dual-core 32-bit LX7 microprocessor,up to 240 MHz.
- 384 KB ROM
- 512 KB SRAM
- Secure boot
- Bluetooth LE: Bluetooth 5, Bluetooth mesh.
- IEEE 802.11b/g/n-compliant.
Marauder is not just firmware for the ESP32; it’s a suite of powerful tools that unlocks its full potential as a WiFi and Bluetooth powerhouse for both offensive and defensive security purposes. Offering a variety of capabilities:
- Offensive Arsenal:
- Network Scanning and Sniffing: Scan for nearby Wi-Fi networks, identify connected devices, and even capture network traffic to understand data flow.
- Vulnerability Assessments: Test the security of Wi-Fi networks and devices by probing for weaknesses like WPS vulnerabilities, open ports, and outdated firmware.
- Deauth Attacks: Disrupt wireless connections by injecting deauthentication packets, effectively “kicking” devices offline.
- Packet Injection: Craft and inject custom packets into wireless networks for advanced manipulation and exploration.
- Man-in-the-Middle Attacks: Intercept and modify communication between devices on a network, potentially gaining access to sensitive information.
- Defensive Shield:
- Wireless Intrusion Detection: Monitor your own network for suspicious activity and identify potential threats like unauthorized devices or hacking attempts.
- Packet Capture and Analysis: Capture and analyze network traffic to understand data flows, identify anomalies, and troubleshoot network issues.
- Penetration Testing: Simulate real-world attacks on your own network to identify and address vulnerabilities before attackers do.
- Wireless Forensics: Analyze captured network traffic for traces of past activity, potentially aiding in investigations or incident response.














There are no reviews yet.