How does BomberCat work?
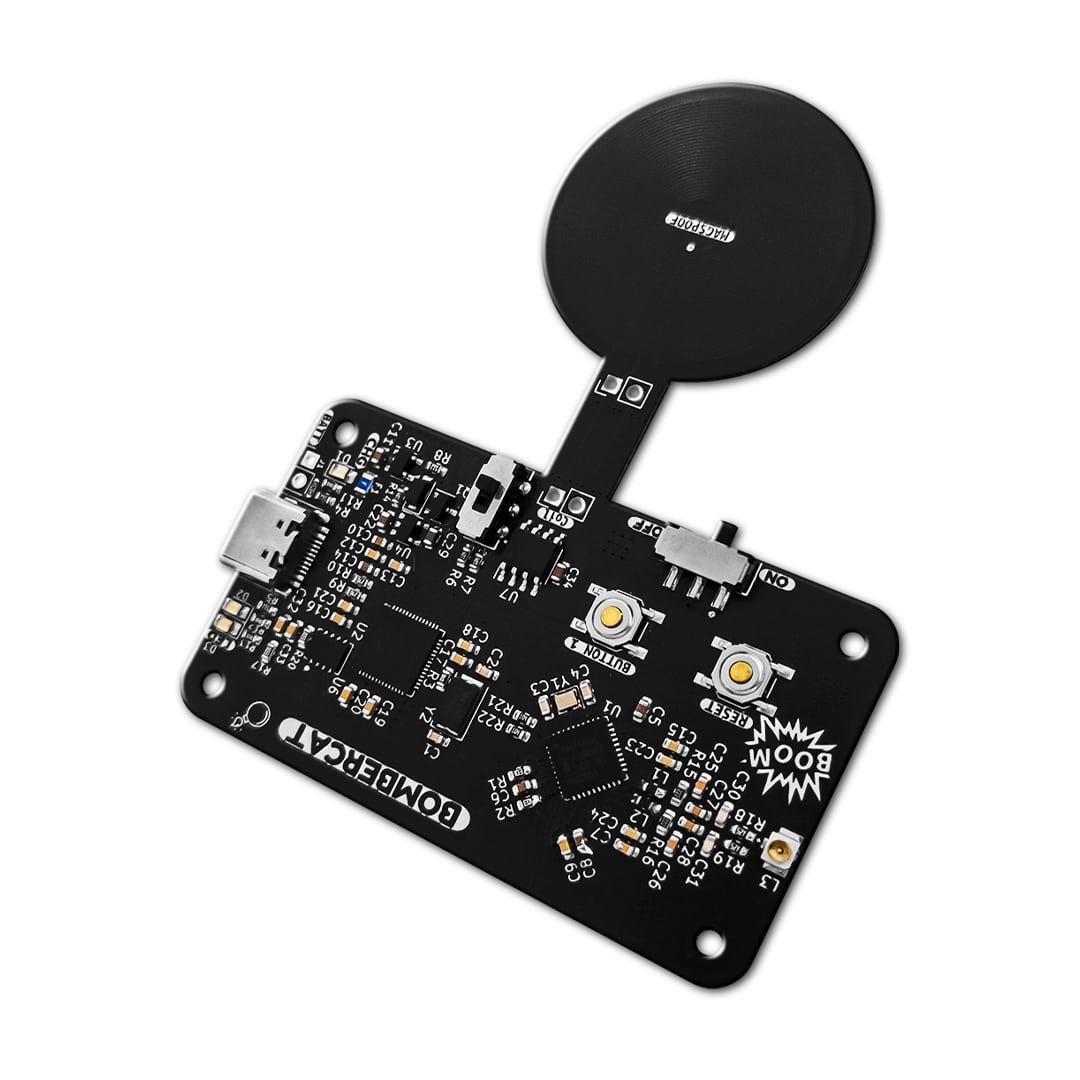
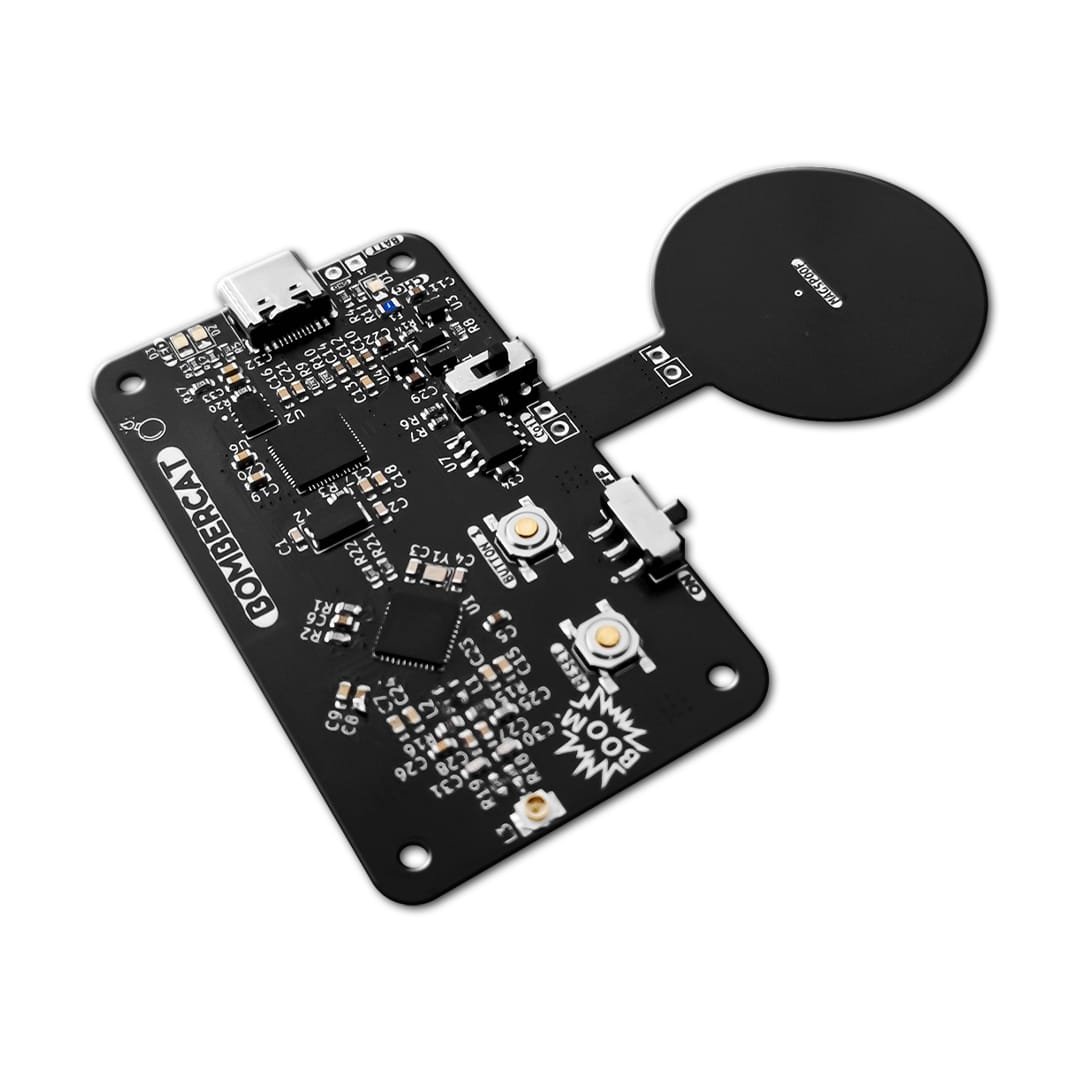
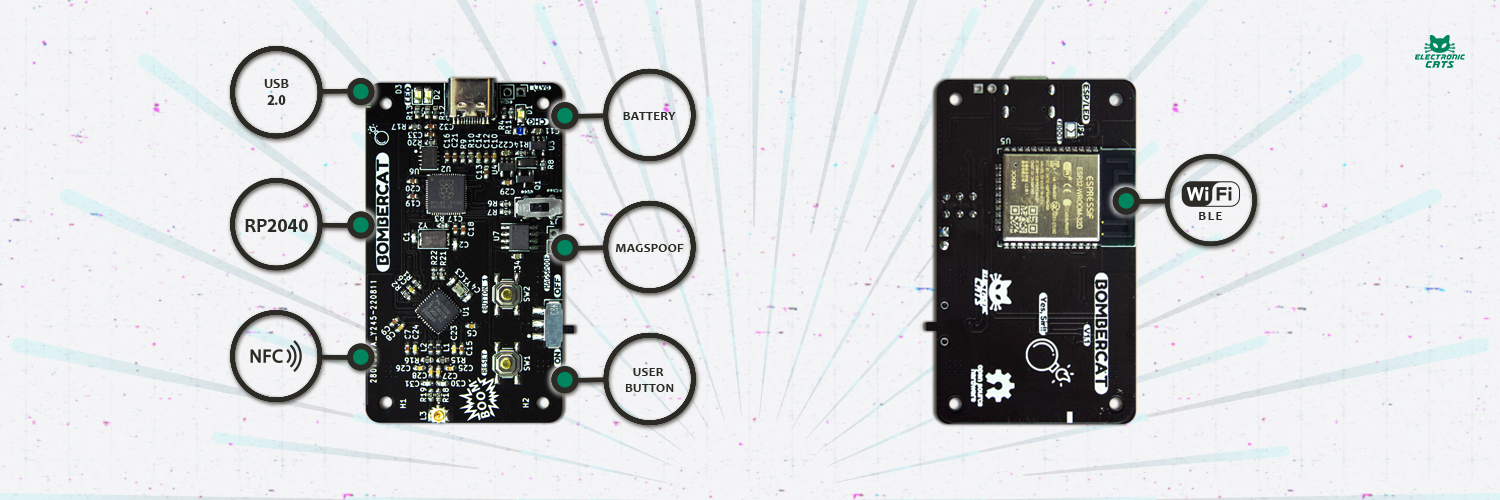
BomberCat is the latest security tool that combines the most common card technologies: NFC technology (Near Field Communication) and magnetic stripe technology used in access control, identification, and banking cards. Specially created to audit banking terminals, and identify NFC readers and sniffing tools, with this tool you can audit, read or emulate magnetic stripes and NFC cards.
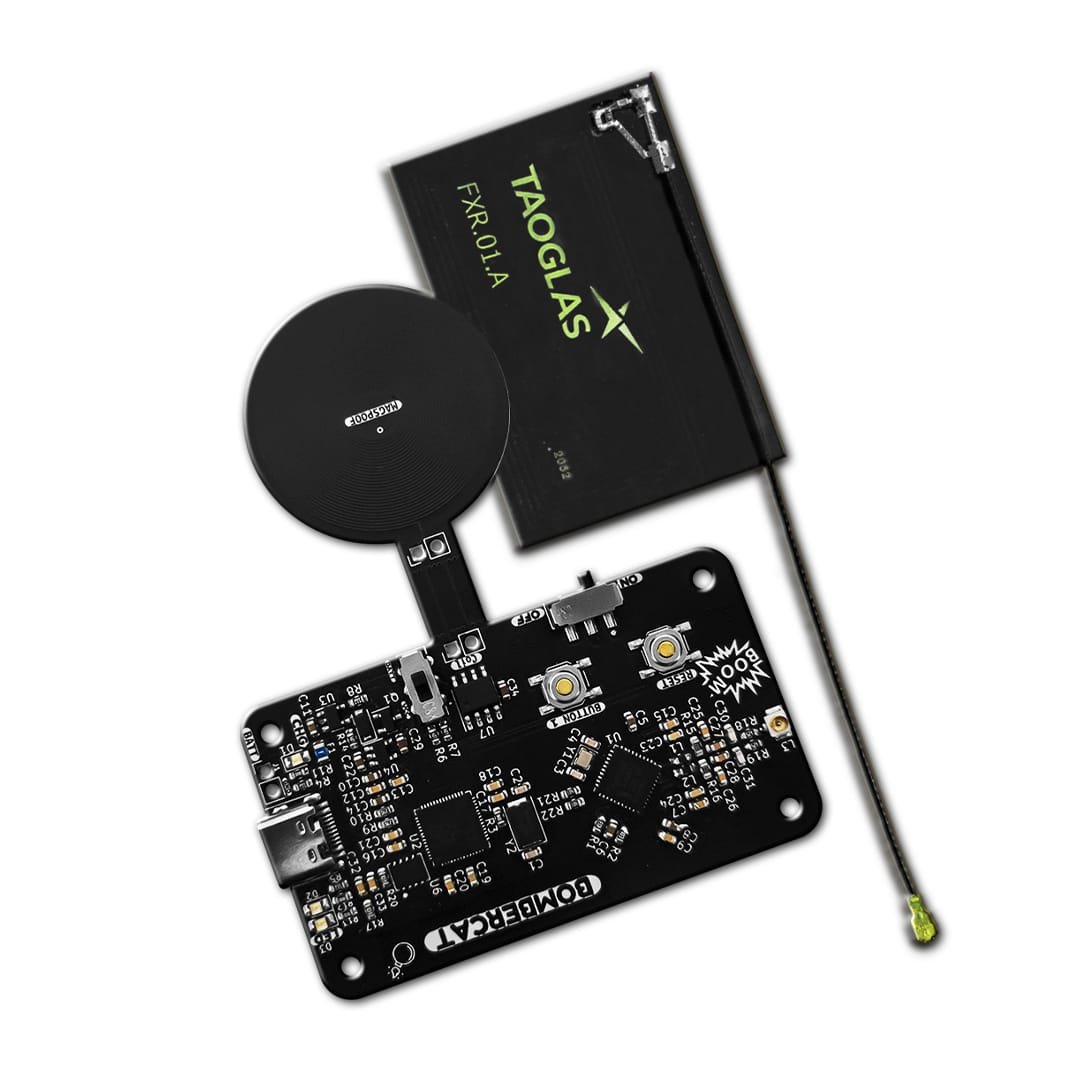
It also has an ESP32 co-processor with WiFiNINA firmware that allows it to make WiFi connections to use with HTTP or MQTT protocols, which will allow relay and spoofing attacks to be tested over long distances or on local web servers.
Applications
BomberCat features an RP2040 MCU working along with the PN7150 (a recent generation NFC chip). The USB interface provided by the RP2040 MCU and the NFC functionality is guaranteed by the PN7150.
BomberCat is designed to be intuitive for users. Easy to program using frameworks such as Arduino, Ciruitpython, and Micropython. We have prepared a series of examples with which you can start experimenting, check out the examples folder.
Card emulation mode: in which BomberCat behaves as a smart card or a tag. In this mode, BomberCat emulates an NFC tag. It does not initiate communication, it only responds to the NFC reader. A typical application of the card emulation mode is how people use NFC on their smartphones to replace several cards, badges, or tags at once (using the same smartphone for RFID access controls, contactless payments, etc). However, card emulation mode is not only beneficial for smartphones but any type of portable device.
Read/Write: in which BomberCat behaves as an NFC reader/writer. In this mode, BomberCat communicates with a passive tag, an NFC smart card, or an NFC device operating in the card emulation mode. It can read or write to a tag (although reading is a more common use case because tags will often be write-protected). In this mode, BomberCat generates an RF field, while a tag or card only modulates it.
Magspoof: for magnetic stripes interaction. Magspoof mode can emulate magnetic stripes cards by emulating the electromagnetic pulses of this type of card.
Characteristics:
- Cortex M0+ processor
- USB C 2.0
- NFC Reader, Card and NFC Forum
- Arduino compatible
- 100% CircuitPython compatible
- UF2 Bootloader
- WIFI (WiFiNINA)
- BLE (ArduinoBLE)
- 1 LEDs status
- Open Hardware
- Magpoof coil
- Battery
- RF protocols supported
- NFCIP-1, NFCIP-2 protocol
- ISO/IEC 14443A, ISO/IEC 14443B PICC, NFC Forum T4T modes via host interface
- NFC Forum T3T via host interface
- ISO/IEC 14443A, ISO/IEC 14443B PCD designed according to NFC Forum digital protocol T4T platform and ISO-DEP
- FeliCa PCD mode
- MIFARE Classic PCD encryption mechanism (MIFARE Classic 1K/4K)
- NFC Forum tag 1 to 5 (MIFARE Ultralight, Jewel, Open FeliCa tag, MIFAREDESFire
- ISO/IEC 15693/ICODE VCD mode
- Includes NXP ISO/IEC14443-A and Innovatron ISO/IEC14443-B intellectual property licensing rights
Disclaimer
BomberCat is a wireless penetration testing tool intended solely for use in authorized security audits, where such usage is permitted by applicable laws and regulations. Before utilizing this tool, it is crucial to ensure compliance with all relevant legal requirements and obtain appropriate permissions from the relevant authorities.
It is essential to note that the board does not provide any means or authorization to utilize credit cards or engage in any financial transactions that are not legally authorized. Electronic Cats holds no responsibility for any unauthorized use of the tool or any resulting damages.











There are no reviews yet.